Shibboleth in Higher Education: Why It’s Still the Gold Standard
When it comes to Single Sign-On (SSO) in higher education, one name comes up again and again: Shibboleth. Despite newer protocols and tools entering the identity management space, universities around the world continue to rely on Shibboleth as a trusted solution.
But why has Shibboleth stood the test of time? And is it still the right choice for modern higher ed IT environments? Let’s explore why Shibboleth remains the gold standard in academia.
What Is Shibboleth?
Shibboleth is an open-source project that provides Single Sign-On (SSO) and federated identity management. It allows users at a university to log in once and securely access multiple applications, both on campus and across federations like InCommon.
Key features include:
- Strong support for SAML authentication
- Integration with identity federations for research and collaboration
- Flexibility to work with legacy and modern applications
- Open-source community support and regular updates
[See our comparison of protocols in SAML vs OAuth vs OpenID Connect for context.]
Why Universities Trust Shibboleth
1. Federation Support
Shibboleth was designed with academic collaboration in mind. Through federations like InCommon, universities can securely share resources and authenticate users across institutions. This makes it an essential tool for research communities.
2. Open-Source Flexibility
Unlike commercial tools, Shibboleth gives universities full control. Institutions can customize configurations, contribute to the project, and avoid vendor lock-in.
3. Proven Track Record
With more than two decades of adoption, Shibboleth has a long history in higher education. IT teams know it, trust it, and can rely on its stability.
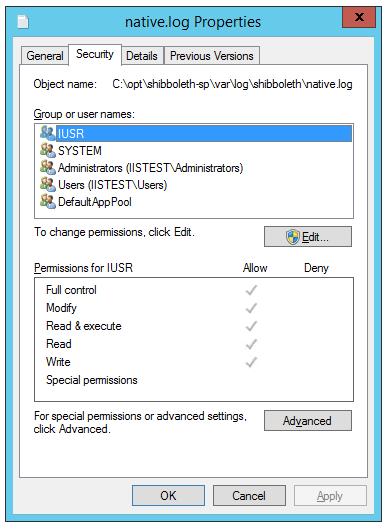
4. Strong Security Standards
Shibboleth supports robust security protocols and configurations. When managed correctly, it meets compliance requirements for FERPA, HIPAA, and GDPR.
5. Community and Ecosystem
The Shibboleth Consortium and its community ensure ongoing support, documentation, and development. This community-driven model has helped the project remain relevant while other identity solutions have come and gone.
Common Challenges with Shibboleth
While Shibboleth is powerful, it’s not without challenges.
- Complex configuration: Initial setup and attribute release policies can be difficult to manage. [See our post on The Top 5 Mistakes Universities Make with SSO.]
- Resource intensive: Smaller IT teams may struggle to dedicate enough time and expertise.
- Integration with modern apps: Many cloud applications are moving toward OAuth and OpenID Connect, requiring hybrid strategies.
Shibboleth in a Modern IT Environment
The reality is that most universities today don’t use Shibboleth alone. Instead, they integrate it alongside other protocols to cover all use cases:
- Shibboleth (SAML) for federation and academic resource access.
- OAuth/OpenID Connect for cloud applications and mobile environments.
[See What Is SSO and Why Your University or Enterprise Needs It for the bigger picture.]
This hybrid approach allows universities to benefit from Shibboleth’s strengths while staying compatible with modern systems.
Conclusion
Shibboleth continues to be the gold standard for higher education because it was built for the unique needs of universities — federation, security, and collaboration. While it requires expertise to configure and maintain, its flexibility and proven track record make it a cornerstone of academic identity management.
At IDM Engineering, we’ve helped universities successfully implement and maintain Shibboleth for research, compliance, and user access.
? Contact us to Book a 4-hour Consultation and ensure your Shibboleth environment is secure, scalable, and ready for the future.